Contents
Protecting patient health information is one of the most critical responsibilities in healthcare technology. Cyber threats are increasing in sophistication, and the consequences of non-compliance can be severe.
According to an IBM report, healthcare recorded the highest average cost per data breach, reaching USD 10.93 million. This highlights the financial, legal, and reputational risks associated with inadequate security measures in electronic health record systems.
The Health Insurance Portability and Accountability Act establishes strict standards for safeguarding protected health information through administrative, physical, and technical safeguards.
For healthcare providers, healthtech startups, and software companies, developing a HIPAA-compliant EHR system requires more than adding encryption or secure login features. It demands a security-first architecture, robust access controls, audit logging, secure data storage, disaster recovery planning, and ongoing risk assessments.
In this blog, we will explain how to develop a HIPAA-compliant EHR system step by step. You will learn about core HIPAA requirements, essential technical safeguards, infrastructure considerations, common development mistakes, and cost factors. Drawing from our 15+ years of experience as a trusted EHR development agency, we have shared insights to help you build a secure, scalable, and regulation-ready system.
What is HIPAA-Compliant EHR Development?
HIPAA-compliant EHR development is the process of building electronic health record systems that meet federal data protection standards. These systems must follow the rules set by the Health Insurance Portability and Accountability Act of 1996. Developers design every component to protect patient health information from unauthorized access. The goal is to create software that delivers clinical value while maintaining regulatory compliance.
HIPAA defines two primary rules that govern EHR platforms. The Privacy Rule controls who can view and share protected health information (PHI). The Security Rule establishes technical, physical, and administrative safeguards for electronic PHI. Both rules carry significant penalties for violations.
Building a compliant system goes beyond adding basic password protection. It requires role-based access controls, end-to-end data encryption, and detailed audit logging. Firms that treat compliance as an afterthought face expensive redesigns and potential legal consequences.
Why HIPAA Compliance is Critical in EHR Development
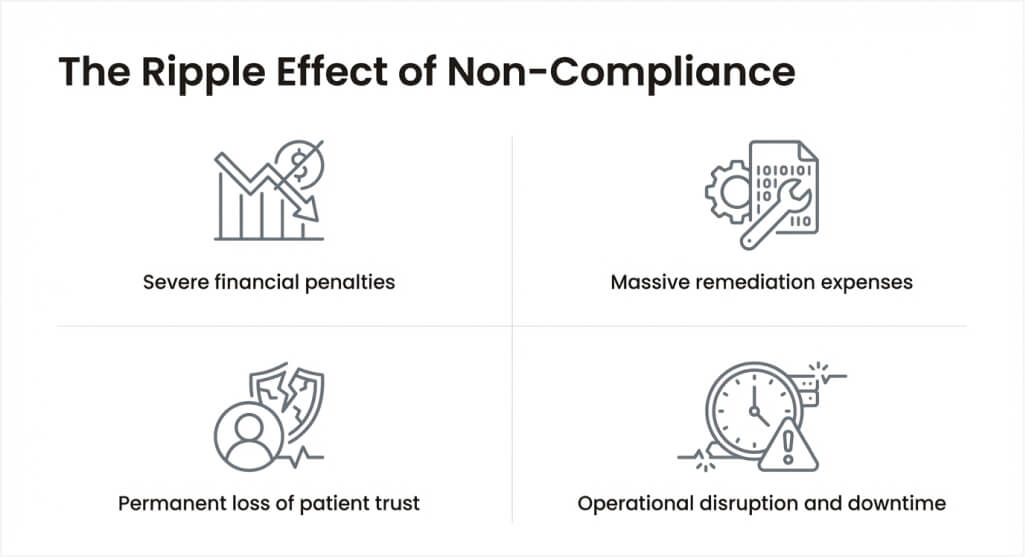
Ignoring HIPAA requirements during EHR development for pediatric care creates serious risks for healthcare providers and their patients. The consequences extend far beyond financial penalties, including operational disruption and reputational damage. The proposed 2025 HIPAA Security Rule update removes the distinction between “addressable” and “required” safeguards. Proactive compliance protects your organization against current and future regulatory shifts.
1. Severe financial penalties for violations
HIPAA fines vary significantly based on the level of negligence involved in each violation. Major breaches can trigger settlements reaching tens of millions of dollars, as demonstrated by enforcement actions from the HHS Office for Civil Rights. For smaller providers, the financial impact can be especially severe—making compliance a critical priority in EHR development for small practices. These costs can devastate small clinics and place significant strain on larger health systems alike.
2. Massive breach remediation expenses
Large-scale healthcare breaches expose millions of patient records and generate enormous financial consequences. Remediation includes forensic investigations, legal fees, and patient notification services. Organizations may also face class-action lawsuits and regulatory settlements, in addition to direct recovery costs. These expenses accumulate rapidly and consume resources meant for patient care.
3. Permanent loss of patient trust
Research consistently shows that a significant percentage of patients would switch providers after a data breach. Trust takes years to build but only moments to destroy. A breach signals that their confidential information was not adequately protected. Rebuilding reputation after a security incident requires sustained effort and investment over an extended period.
4. Operational disruption and downtime
Breaches force providers to shut down systems during investigation and recovery. Clinical workflows halt when staff cannot access patient records. Identifying and containing a healthcare breach often takes months, disrupting operations throughout the entire process. The ripple effects impact scheduling, billing, and care delivery long after the initial incident.
Organizations that invest in HIPAA compliance from the start avoid these devastating outcomes. Proactive security costs far less than reactive breach management. Industry research consistently shows that non-compliance costs significantly more than investing in proper safeguards upfront. Building it right the first time is always the smarter financial decision.
Turn HIPAA Requirements Into a Secure EHR System
Work with an experienced EHR development company that understands healthcare regulations and builds compliance-ready software from day one.

Core HIPAA Requirements for EHR Systems
Understanding HIPAA’s regulatory framework is essential before writing a single line of code. The law establishes clear expectations for how providers must handle electronic health data. Missing even one safeguard can expose the entire system to regulatory action. The following breakdown covers the most critical mandates every EHR platform must satisfy.
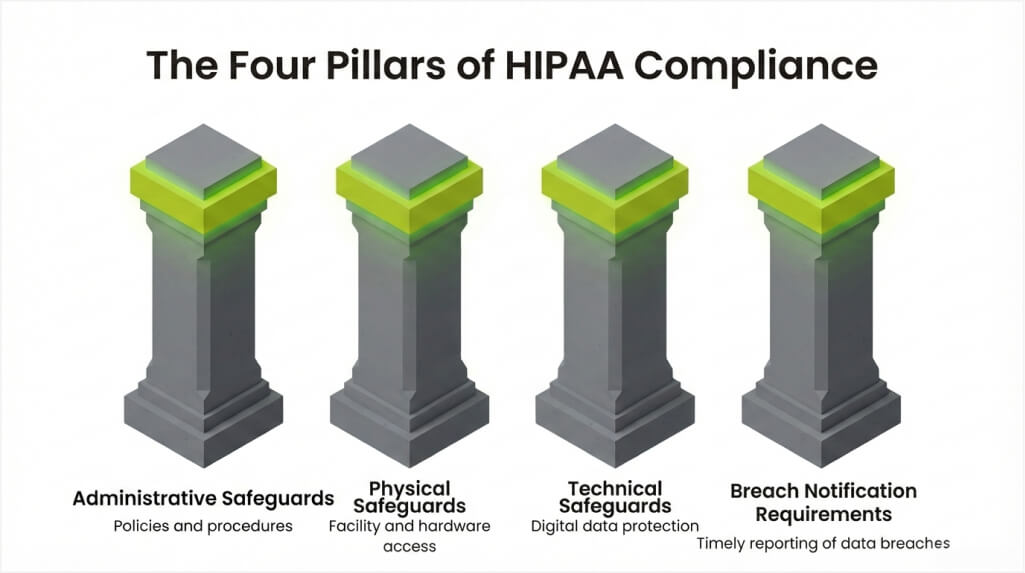
1. Administrative safeguards
Administrative safeguards establish the policies and procedures that govern data protection practices. These controls define how organizations manage security across their operations.
- Conduct regular risk assessments to identify vulnerabilities in systems and processes.
- Develop and enforce workforce security policies for all employees with PHI access.
- Create incident response plans that outline steps for detecting and addressing breaches.
- Implement security awareness training programs for every staff member.
- Establish business associate agreements (BAAs) with all third-party vendors handling PHI.
2. Physical safeguards
Physical safeguards protect the hardware, facilities, and equipment that store or transmit electronic PHI. These controls prevent unauthorized physical access to sensitive data.
- Restrict facility access using badge systems, biometric readers, or security personnel.
- Maintain device and media controls for laptops, mobile devices, and removable storage.
- Establish proper disposal procedures for hardware containing electronic PHI.
- Monitor physical access points with surveillance systems and visitor logs.
3. Technical safeguards
Technical safeguards form the backbone of HIPAA-compliant EHR software. These controls protect data during storage, transmission, and access.
- Deploy access controls that limit PHI visibility based on user roles and responsibilities.
- Implement audit controls that record every action performed on electronic health data.
- Ensure data integrity mechanisms that prevent unauthorized alteration of PHI records.
- Enforce transmission security through encryption protocols for all data in transit.
- Authenticate every user using unique identifiers and multi-factor authentication.
4. Breach notification requirements
HIPAA mandates specific actions when a breach of unsecured PHI occurs. Organizations must notify affected individuals, the HHS, and sometimes the media.
- Notify affected patients within 60 days of discovering a breach.
- Report breaches affecting 500 or more individuals to HHS and local media outlets.
- Document smaller breaches and submit annual reports to the Office for Civil Rights.
- Maintain detailed records of all breach investigations and corrective actions taken.
- Conduct post-breach assessments to strengthen safeguards and prevent repeat incidents.
Adhering to these core HIPAA requirements is fundamental to building secure and compliant EHR systems across healthcare domains. However, implementation strategies often vary by specialty, as seen in solutions like EHR system development for dental clinics, where workflow-specific safeguards and integrations play a critical role in ensuring both usability and compliance.
Similarly, specialized fields demand tailored approaches to data protection and patient privacy. For example, EHR development for mental health highlights the need for enhanced confidentiality controls and sensitive data handling. A compliance-first mindset, combined with domain-specific customization, ensures your EHR system remains secure, scalable, and aligned with regulatory expectations.
Essential Security Features for HIPAA Compliant EHR Software
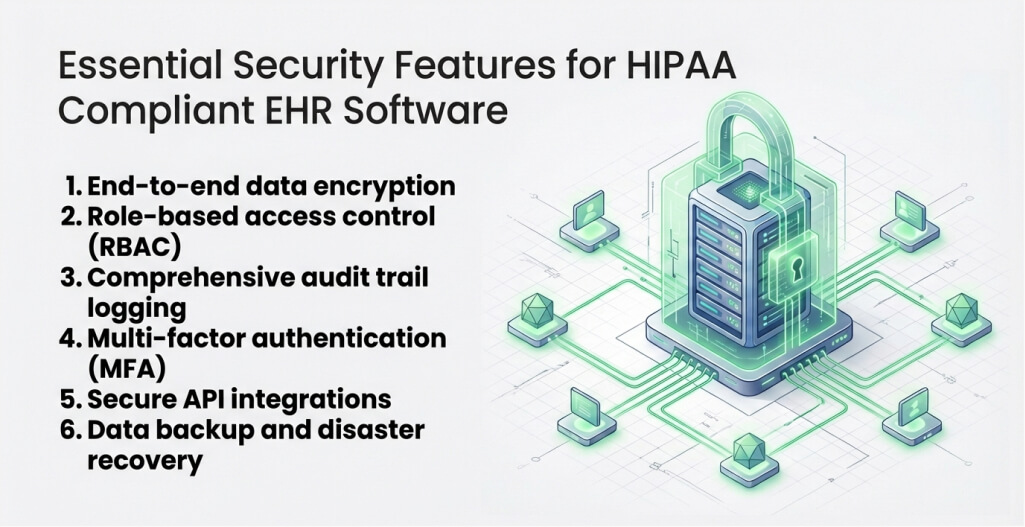
Security features transform regulatory requirements into functional system capabilities. Every HIPAA-compliant EHR platform must include specific technical controls to protect patient data. The best systems balance strong security with intuitive clinical workflows, which makes HIPAA-compliant EHR development essential from the earliest design stages. Below are the features your EHR system absolutely must include.
1. End-to-end data encryption
Encryption converts patient data into unreadable code without the proper decryption key. AES-256 encryption protects data at rest in databases and file systems. TLS 1.2 or higher secures data during transmission between systems. Every piece of PHI must remain encrypted throughout its entire lifecycle.
2. Role-based access control (RBAC)
RBAC restricts system access based on each user’s job function and clinical responsibilities. Physicians have access to full patient records, while billing staff see only financial data. Nurses view treatment details relevant to their care assignments. Administrators manage system configurations without viewing individual patient records.
3. Comprehensive audit trail logging
Audit trails capture every interaction with patient data inside the EHR platform. The system records who accessed which records, when, and what actions they performed. These logs support compliance audits and forensic investigations after security events. Tamper-proof logging prevents bad actors from covering their tracks.
4. Multi-factor authentication (MFA)
MFA requires users to verify their identity through two or more independent methods. A password combined with a biometric scan or a one-time code adds a critical layer of security. This feature blocks unauthorized access even when login credentials are compromised. The proposed 2025 HIPAA Security Rule update makes MFA mandatory for all covered entities.
5. Secure API integrations
EHR platforms connect with labs, pharmacies, imaging centers, and billing systems through APIs. Every integration point must enforce authentication, encryption, and data validation protocols. Insecure APIs create entry points for attackers targeting the broader healthcare network. FHIR-based APIs with OAuth 2.0 authorization provide the strongest security for integration.
6. Data backup and disaster recovery
Regular automated backups protect against data loss from hardware failures, ransomware, or natural disasters. Backup data must receive the same level of encryption protection as primary storage. Disaster recovery plans define procedures for restoring operations within acceptable timeframes. Testing these plans regularly ensures they work when providers need them most.
These features represent the minimum security baseline for any HIPAA-compliant EHR system. To implement them effectively, organizations must also understand how to find experienced EHR developers who can address complex security and compliance requirements. A strong security architecture, tailored to your specific risk profile, reduces the likelihood of breaches and demonstrates a clear commitment to regulatory compliance.
Implement Advanced Security in Your EHR
Our healthcare software experts design EHR systems with encryption, role-based access control, audit trails, and secure cloud infrastructure.
Steps to Build a HIPAA Compliant EHR System
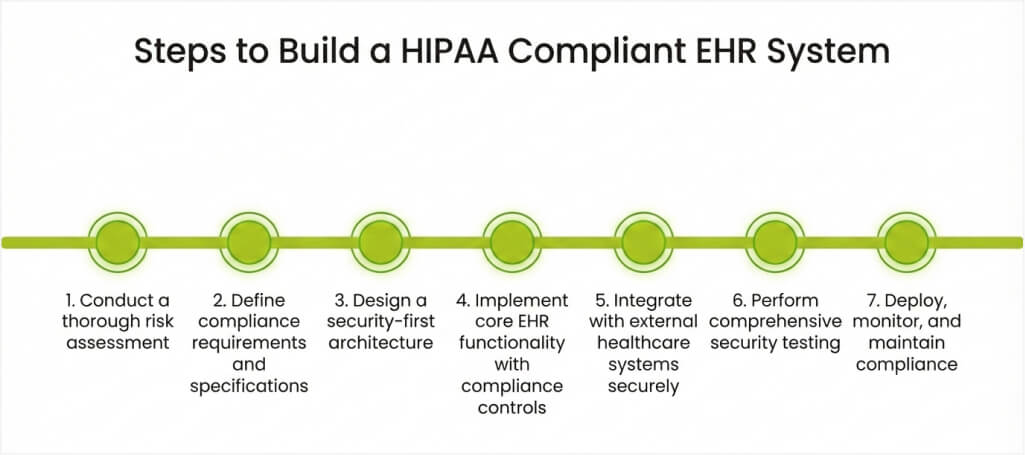
Building a HIPAA-compliant EHR system requires a structured, phased approach from concept to deployment. Skipping steps or rushing through critical phases leads to compliance gaps and security vulnerabilities. You can partner with an experienced healthcare software development company like Space-O Technologies to build your software. Such agencies bring years of experience in developing HIPAA-compliant healthcare solutions.
Step 1: Conduct a thorough risk assessment
Begin by identifying all potential threats to the confidentiality, integrity, and availability of PHI. Map every data flow within the proposed system to understand where vulnerabilities could emerge. Document existing security controls and identify gaps that need to be addressed. This assessment forms the basis for all subsequent design and development decisions.
Step 2: Define compliance requirements and specifications
Translate HIPAA rules into specific technical and operational requirements for your EHR platform. Create detailed security specifications covering encryption standards, access control models, and logging mechanisms. These specifications guide your development team throughout the entire build process.
Step 3: Design a security-first architecture
Architect the system with security embedded into every component rather than bolted on afterward. Design separate data layers for PHI storage with strict access boundaries. Plan encryption strategies for data at rest, in transit, and during processing.
Step 4: Implement core EHR functionality with compliance controls
Build clinical workflows, patient management features, and documentation tools alongside security mechanisms. Integrate RBAC into every module so access restrictions function from the first release. Embed audit logging into all data operations to capture a complete activity history.
Step 5: Integrate with external healthcare systems securely
Connect your EHR with laboratories, pharmacies, insurance payers, and imaging centers using secure protocols. Implement HL7 FHIR standards for interoperability with other healthcare platforms. Validate every EHR software integration endpoint against HIPAA security requirements before activation.
Step 6: Perform comprehensive security testing
Execute penetration testing, vulnerability scanning, and code reviews across the entire platform. Simulate breach scenarios to validate incident response procedures and recovery capabilities. Document all findings and remediate every identified vulnerability before deployment.
Step 7: Deploy, monitor, and maintain compliance
Launch the system with continuous monitoring tools that track access patterns and security events. Schedule regular compliance audits to verify that safeguards remain effective over time. Update security controls as HIPAA regulations evolve and new risks emerge.
Following these steps creates a strong compliance posture that withstands regulatory scrutiny—an approach commonly adopted by the best EHR development companies to ensure security and reliability. Each phase produces documentation that proves your organization takes data protection seriously, and a methodical development process remains your strongest defense against breaches and penalties.
Common HIPAA Compliance Challenges in EHR Development
Even experienced development teams encounter obstacles when building HIPAA-compliant healthcare software—especially during early-stage validation through MVP development for EHR software, where compliance must be balanced with speed. Regulatory complexity, evolving threats, and operational pressures create persistent challenges. Recognizing these hurdles early enables proactive mitigation strategies. Below are the most common issues and practical solutions to overcome them.
Challenge 1: Balancing security with clinical usability
Strict security controls can slow down clinical workflows and frustrate healthcare providers. Physicians need rapid access to patient information during consultations and emergencies. The challenge is protecting data without creating barriers to patient care.
How to overcome this challenge
- Design context-aware authentication that adjusts security levels based on clinical urgency.
- Implement single sign-on (SSO) solutions that reduce login friction across applications.
- Conduct usability testing with actual clinicians to identify workflow bottlenecks early.
- Create emergency access protocols that grant temporary elevated permissions with full audit logging.
Challenge 2: Managing PHI across cloud environments
Cloud-hosted EHR platforms distribute patient data across multiple servers and geographic regions. Shared infrastructure introduces risks from neighboring tenants and cloud provider access. Organizations must independently verify that cloud providers meet HIPAA requirements.
How to overcome this challenge
- Select cloud providers that offer HIPAA-compliant infrastructure and are willing to sign BAAs.
- Implement client-side encryption so data remains protected even from the cloud provider.
- Use dedicated hosting environments instead of shared tenancy for the most sensitive PHI.
- Monitor cloud access logs continuously to detect unauthorized or suspicious activity.
Challenge 3: Keeping pace with evolving regulations
HIPAA requirements change through new rules, guidance documents, and enforcement trends. The proposed 2025 Security Rule update introduces significant new mandates. Falling behind on regulatory changes creates compliance gaps that auditors will identify.
How to overcome this challenge
- Assign a dedicated compliance officer to monitor regulatory updates and industry guidance.
- Design modular security architectures that allow rapid implementation of new controls.
- Schedule quarterly compliance reviews to assess system alignment with current requirements.
Challenge 4: Securing third-party integrations and vendor relationships
Hacking and IT incidents are a leading cause of healthcare data breaches. Many of these breaches originate through third-party vendor connections and insecure integration points. Every external system that interacts with an EHR platform expands the potential attack surface. Managing vendor security requires continuous monitoring and diligence beyond the initial assessment.
How to overcome this challenge
- Require all vendors to sign comprehensive BAAs before granting any access to PHI.
- Conduct annual security assessments of every third-party integration partner.
- Implement API gateways that monitor, throttle, and log all external data exchanges.
- Maintain a vendor risk registry that continuously tracks the security posture and compliance status.
Addressing these challenges proactively significantly strengthens your platform’s compliance posture. Many organizations choose to outsource EHR software development to experienced partners who can anticipate risks and implement robust safeguards from the start. This investment in overcoming challenges pays dividends by reducing breach risk, improving system resilience, and making audits smoother.
Overcome HIPAA Compliance Challenges With Expert EHR Developers
With 15+ years of healthcare software development experience and 1200+ clients served, Space-O Technologies helps you design and deploy fully HIPAA-compliant EHR solutions with confidence.
How Much Does it Cost to Build a HIPAA-Compliant EHR System?
Building a HIPAA-compliant EHR system requires significant investment across multiple categories. EHR software development costs vary based on system complexity, security requirements, and organizational scale. Understanding these factors helps you allocate budget effectively and avoid surprises. Below is a breakdown of the primary cost drivers.
1. Security infrastructure and encryption
Implementing enterprise-grade encryption, key management systems, and secure hosting environments forms a major cost category. Cloud providers charge premium rates for HIPAA-compliant hosting configurations. Budget $50,000 to $200,000 for initial security infrastructure, depending on scale.
2. Compliance consulting and legal review
HIPAA regulations demand expert interpretation for proper implementation. Legal teams review BAAs, privacy policies, and breach notification procedures. Expect to invest $25,000 to $100,000 for thorough compliance and legal support.
3. Development and testing resources
Secure EHR development requires specialized engineers with domain knowledge in healthcare. Building RBAC, audit logging, and encryption features adds development time beyond standard functionality. Custom EHR platforms typically cost $100,000 to $ 500,000 or more for complete development.
4. Ongoing compliance maintenance
HIPAA compliance is not a one-time achievement. Regular risk assessments, security updates, and staff training require annual budgets. Plan for $30,000 to $100,000 annually in ongoing compliance maintenance costs.
5. Certification and audit preparation
Organizations pursuing HITRUST certification or SOC 2 compliance face additional preparation costs. Audit preparation involves documentation, remediation, and third-party assessment fees. Budget $20,000 to $75,000 for initial certification efforts.
| Cost Category | Small Platform | Mid-Size Platform | Enterprise Platform |
|---|---|---|---|
| Security Infrastructure | $50,000 – $100,000 | $100,000 – $150,000 | $150,000 – $200,000+ |
| Compliance Consulting | $25,000 – $40,000 | $40,000 – $70,000 | $70,000 – $100,000 |
| Development and Testing | $100,000 – $200,000 | $200,000 – $350,000 | $350,000 – $500,000+ |
| Annual Maintenance | $30,000 – $50,000 | $50,000 – $75,000 | $75,000 – $100,000 |
| Certification | $20,000 – $35,000 | $35,000 – $55,000 | $55,000 – $75,000 |
The right investment in HIPAA-compliant EHR development protects your organization from far greater costs. A well-funded compliance program reduces breach risk and strengthens patient confidence. Strategic spending during the build phase prevents expensive remediation after deployment.
Develop a Secure and Compliant EHR System with Space-O Technologies
Developing a HIPAA-compliant EHR system is not just about meeting regulatory requirements. It is about building a secure foundation that protects patient data and ensures safe interoperability through EHR integration services. From implementing safeguards to designing encrypted data flows and audit mechanisms, every layer must prioritize compliance.
However, achieving full HIPAA compliance while maintaining scalability, usability, and interoperability requires deep healthcare domain expertise. Security gaps, improper architecture decisions, or incomplete compliance documentation can lead to significant financial penalties and reputational damage. A strategic security-first EHR system modernization and development approach is essential.
With 15+ years of healthcare software development experience and 1200+ clients served, Space-O Technologies specializes in building secure, scalable, and fully HIPAA-compliant EHR systems. Our team understands healthcare regulations, interoperability standards, and modern cloud security frameworks to deliver audit-ready solutions tailored to your clinical and operational needs.
If you are planning to develop a new EHR system or modernize an existing one, aligning your technology with clinical workflows and compliance requirements is essential. A well-planned approach helps minimize risks and ensures long-term scalability. That’s why many healthcare organizations prefer to hire EHR software developers with proven domain experience. Consult our healthcare software experts today and let us help you build a secure, compliant, and future-ready EHR solution.
FAQs About HIPAA Compliant EHR Development
1. What makes an EHR system HIPAA compliant?
A HIPAA-compliant EHR system implements all required administrative, physical, and technical safeguards defined by federal regulations. This includes data encryption at rest and in transit, role-based access controls, comprehensive audit trails, and multi-factor authentication. The system must also maintain business associate agreements with all third-party vendors that access protected health information.
2. How long does it take to build a HIPAA-compliant EHR system?
Development timelines vary based on system complexity and feature scope. A basic HIPAA-compliant EHR platform typically takes 6 to 9 months to implement. Mid-complexity systems with custom workflows and multiple integrations take 9 to 14 months. Enterprise-grade platforms may require 14 to 18 months or longer.
3. Can cloud-hosted EHR systems be HIPAA compliant?
Yes, cloud-hosted EHR systems can achieve full HIPAA compliance when configured properly. The cloud provider must sign a business associate agreement and offer HIPAA-compliant infrastructure. Leading providers like AWS, Microsoft Azure, and Google Cloud offer HIPAA-eligible services designed for healthcare workloads.
4. What happens if an EHR system fails a HIPAA compliance audit?
Failed audits can result in corrective action plans, financial penalties, and increased regulatory scrutiny. The HHS Office for Civil Rights may impose fines ranging from $100 to $50,000 per violation. Organizations must address identified deficiencies within specified timeframes. Repeated failures or willful neglect can trigger penalties of up to $1.5 million annually per violation category.
5. How often should HIPAA compliance be reassessed for an EHR system?
Organizations should conduct formal HIPAA risk assessments at least annually. Additional assessments are necessary after major system updates, new integrations, or security incidents. Continuous monitoring should supplement annual reviews to detect emerging threats in real time. Regular reassessment ensures your EHR platform stays aligned with evolving regulatory requirements and threat landscapes.
6. What is the difference between HIPAA compliance and HITRUST certification?
HIPAA compliance means meeting the minimum federal requirements for protecting electronic health information. HITRUST certification goes further by validating security controls against a comprehensive framework that incorporates HIPAA, NIST, and other standards. Many healthcare organizations pursue both to demonstrate a higher level of security maturity to partners and stakeholders.



