IoT Application Development Company
Looking for the top IoT app and web development company? Want to hire the best IoT developers? At Space-O, we have an in-house team of experienced IoT developers, who have experience in delivering custom IoT-based solutions from scratch. Use this form and tell us about your requirements.
Let’s Discuss Your IoT Project
Internet of Things Solutions & Development
Today, Internet of Things has gone from being just another concept to a brilliantly woven digital revolution that has impacted our daily lives. This advanced technology connects people, machines, processes, and systems onto one technology-enabled network. A number of enterprises and organizations are ready to unleash the potential of this powerful technology that will redefine the way we interact with other humans, machines, and devices.
Space-O Technologies offers technologically advanced Internet of Things (IoT) solutions and application, allowing your business to get maximum benefits of IoT technology. Here, we build apt IoT solutions that are dependent on the nature of need, and the extensiveness of the enterprise.

“Shot Stats” – an IoT-based Application Developed by Us
Our IoT expert team has successfully developed sports tracker device, called Shot Stats, connected with a mobile app to track a tennis players’ performance, after every session.
The custom IoT app design in the device portrays a Spin feature that helps users to collect data by the wearable device, showing how much did the tennis ball spin and in which patterns and styles. Focusing on delivering the options from where one can see specific statistics on peculiar styles they have practiced, including Overhead, Backhands, Forehands, and Serves.
Advantages of IoT Solutions & Application
Adopting IoT solutions and application can benefit your business in many ways like
- Real-time effective decision making
- Automated and optimized processes
- Enhanced processes in complex scenarios
- Optimized use of resources
- Improved marketing automation
- Smart and enhanced supply chain
- Better revenue generation
Different IoT Services We Offer
IoT Solution Development Consulting
Looking for a consulting service before finalizing a project? Talk to our tech consultants who have experience in delivering IoT-based solutions.
KW- IoT Technology Solutions
Our IoT app developers will help you to get a right IoT solution and architecture for your business. We deliver flexible strategies, blended with high-security to manage new and diverse IoT devices.
IoT Architecture Development
We work side-by-side with our clients to know the exact architect needed to connect their devices seamlessly.
IoT Module Development
Once, you choose the right technology, we will help you to develop specific IoT module for your business, helping you to reach your goal and make the most of IoT technology.
IoT Testing
Our IoT experts offers advance quality IoT testing service, ensuring that devices/system connected operate based on the data that is available. We ensure security, performance and compatibility, making our solution bug-free.
IoT Support & Maintenance
We have a technical team. This team will assist you, in case, if you have any confusion or question regarding the solution.
Want to Build an IoT Application?
With years of experience we develop robust IoT applications for any industry. Let’s discuss your idea and various IoT solutions we offer to help your business grow.
Clients Love Space-O Technologies
Project Summary
AI System Development for Gift Search Company
Space-O Technologies has developed an AI system for a gift search company. The team has built a recommendation engine, implemented dynamic pricing, and created tools for personalized marketing campaigns.
Project Summary
AI System Development for Christian Church
Space-O Technologies developed a private AI system for a Christian church. The team built a system capable of uploading research information, allowing other church workers to query information in a natural way.
Project Summary
Mobile App Dev & UX/UI Design for Behavioral AI Company
Space-O Technologies has designed and developed a mobile app for a behavioral AI company. The team is responsible for integrating patient management features, appointment scheduling, and communication tools.
Project Summary
POC Design & Dev for AI Technology Company
Space-O Technologies developed the POC of an AI product for life coaching conversations. Their work included wireframing, app design, engineering, and branding.
IoT Projects & Solutions Developed by Us

Revolutionize your tennis game
A sensor that instantly analyzes your tennis swing like never before. You can track it with a mobile application.

The smart way to monitor temperature
Tempi is a simple Bluetooth device that provides accurate temperature and humidity data on your smartphone.

Automatic Entry System For Paid Parking Lots
Ezepark is the most advanced parking management solution, including Bluetooth-controller, mobile app, iBeacon and web system that help parking owners to automate their parking lots access.

Interactive Mobile App With Vibration Machines Through Bluetooth LE
HyperVibe is an interactive mobile application with vibration machines, allowing users to get control of the vibration machine with 38 exercise programs, featuring over 100 exercise videos.
An IoT based Special Adapter Device For Military Laser Rangefinder
Serial2BLE Converter is an IoT-based special adapter device that allows to re-transfer data from a Serial Port wire connection to mobile app through Bluetooth LE. This device can be used with military laser rangefinder.
Our Developed Apps Have Been Featured In
Why Choose Space-O Technologies?
98%
Success Score on Upwork
4400+
Apps Live on App Stores
1000+
Jobs Completed on Upwork
55+
Unique Feature Implemented
100+
Small and Large Innovation
200+
Mobile App Developers
30M+
App Downloads
14+
Years of Experience
1200+
Clients Worldwide
Want to Discuss Your IoT Software Requirements?
Space-O is a leading software development agency and we develop IoT applications as per your business requirements. Validate your idea with us.
IoT Application Development Process We Follow
Validating Your Idea
- Get in touch with you
- Understand your requirements
- Validating your idea
Wireframing and Prototype
- Understand a user flow
- Create a wireframe
- Create a prototype
Choose Hardware
- Understanding the requirements
- Select appropriate hardware
- Finalize and test hardware
IoT Solution Development
- Front-end Development
- Back-end Development
- Connecting with Hardware
Testing
- Web and app solution testing
- Checking hardware compatibility
- Get your final approval
Deploy & Monitor
- Deploy the solution
- Transfer the code ownership
- Solution maintenance and support
Industries We Serve
Photo & Video
Entertainment
Transportation & Logistics
Banking & Finance
Travel & Tourism
Our Valuable Clients
Appreciation from Clients


Steve
USA
I would like to thank the entire Space-O team for helping us with our photo editing app. We have been working with other developing teams before, and we were able to find Space-O. And all the other developers failed to deliver all great working apps for us. Space-O helped to design the app in a very user-friendly way. They helped us to navigate solutions for the app. And overall went above and beyond with our request.


Olivia Grande
USA
This was the first app I’ve ever developed and they been extremely helpful every step of the way, answering questions, writing recommendations, and tips. If you’re looking for a high-quality app, definitely go with Space-O technologies.

Aamir Jaffar
Kingdom of Saudi Arabia
I hired them for a BA assignment for a project. They did a fantastic job. Quite professional and also good at making the customer understand non technical aspects. Put their mind to think like the customer. A guy named Jaimin was assigned as the work lead and really appreciate his knowledge, understanding customer perspective on the assignment and come up with very valid suggestions. Recommended for mobile app development.

Riccardo Petrachi
United Kingdom
We searched online for app developers that had an extensive experience in mobile app development as well as a strong presence in the market. We chose Space-O specifically because of the up-close experience we had with another app they had developed and we wanted to achieve the same high level of standards, quality, and satisfaction. We were looking for brilliant experts and we found them.

Ashton Asherian
USA
Space-O Technologies showed genuine interest in the project. The efficient team delivered quality results at a cost-effective price. We wanted to develop a minimum viable product that would be ready for scalability. It was a great experience working with them. We are so happy that we had the chance to meet Space-O. We love their work. Their project management and structure were amazing. The team loved what they were doing. There was passion behind every single piece of work.

Tom Asare
Ghana
The app was successfully launched and fulfilled original expectations. The Space-O Technologies team was communicative and effective in completing the project. The app is available in the Google Play store, and we’re thrilled with the final product. They were a highly efficient team to work with. They were strong communicators—whenever I had an issue they were available. Additionally, they were timely in getting deliverables to us.

Nick Power
Australia
Eugene, Vlad, Jigar and their respective teams have been fantastic on all the various apps they have worked on and developed for us over the past 18 months. They are always proactive, responsive to questions and consistently provide top quality development and design work. The use of Skype, email and their own project management tool also makes it easy to keep track on how a project is progressing. I would highly recommend Space-O Technologies for any iOS development or design.

Mark
USA
I can't say enough about how great of a partner Space-O has been to work with over the past year. They were always pushing the project forward and ensuring quality checks at every turn, even pieces of my app that I should have caught before sending to development. Will definitely be referring any clients of mine to Space-O and will have them first on my list of partners to work with.

Ali Husainzada
USA
I value the support that Space-O Technologies has offered. Their team is very receptive to making adjustments and improvements. Their team had no issues with change requests and their project manager always provided great solutions. Furthermore, their commitment to client success and fair pricing makes them the go-to partner for future projects.
Frequently Asked Questions About IoT Solution Development
I want to develop an app for IoT, but unaware of the required steps I should take.
Don’t worry, we are a leading Internet of Things app development company and dedicated to offering technologically advanced IoT solutions and applications, allowing you to get maximum benefits of this technology. Just share your requirements with us and our IoT experts will suggest the best possible solution for your business.
Is there any process you follow to keep my app idea confidential?
Yes, of course. We sign a non-disclosure agreement with our all clients to ensure that their shared app idea is safe and secure with us.
Do I own the ownership and the code of my application?
Yes, the ownership and the code of your IoT application and software solution will belong to you. We will not have any right on the code of your app. In case, if you want a partnership or joint venture, then there will other options for you.
How many IoT mobile apps have been developed by you?
We have developed over 30 IoT mobile apps and software solutions. Here are some of our popular and successful IoT mobile apps:
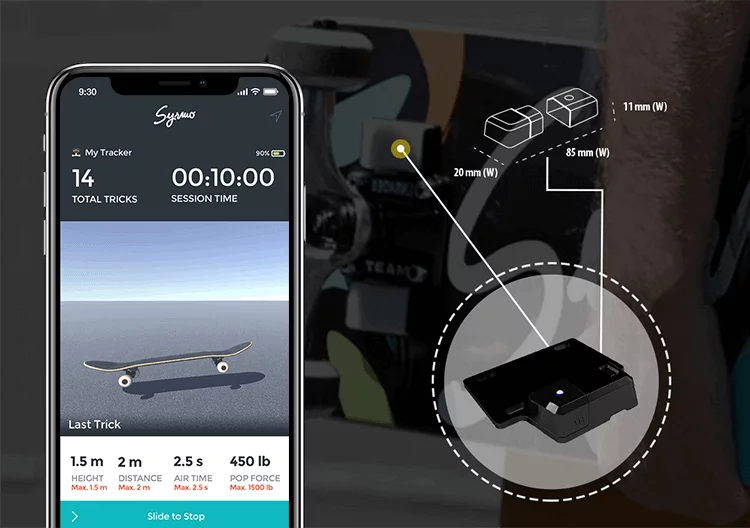
- Syrmo
- MyTempi
- Hypervibe
Here, you can explore all the IoT app development projects that we have successfully handled.
Do you have flexible hiring models for IoT apps development?
Yes, we offer different hiring options, including fixed, hourly, dedicated and on-site team hiring models, so we will be suggesting the one that best meets your project requirements.
How you allocate the resources for my Internet of Things development project?
Depending on your app’s idea and the selected hiring model, we will be allocating the best sources for your IoT software development project.
Can I select my team for my IoT app development project on my own?
Yes, of course. You can select your own team of the internet of things developers, designers, and quality analysts as per your preference and requirement. We will be sharing resumes of the selected IoT programmers and other required team members. From these resumes, you can select them, take interviews (if require) and they will work dedicatedly on your project.
Will I be getting a regular update from you about my project?
Yes, we assign one project manager who will be sharing regular updates with you about the project progress. In case of any query, you can feel free to ask him.
Do you use any project management tool to manage my project?
Yes, we will be using the Basecamp project management tool that we will share with you. Through this tool, you will be stay updated with your project progress on a daily basis.
Will you assist me to launch my IoT app on the App Stores?
Yes, we will deploy your IoT app on the App Stores (Google Play Store and Apple App Store) as our mobile app development process. So, don’t worry about the app deployment part, we will take care of it.
Will I be getting any support after project completion?
Yes, we will be giving 3-months free technical support after we deliver the project to you. In case, if you face any technical issue, feel free to communicate with us.

